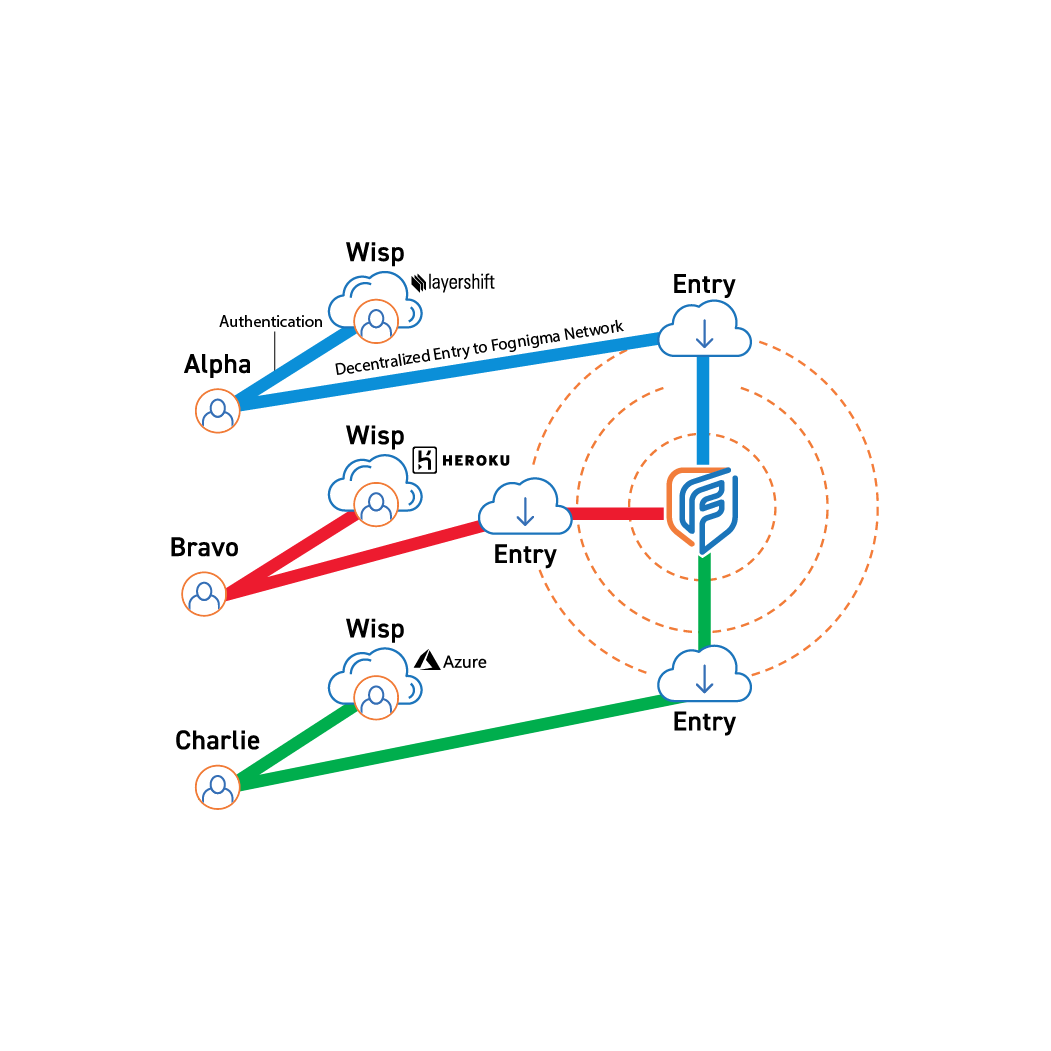
Wisps are cloud based instances that hold user access and token information to allow users and devices to authenticate with the system without communicating with the central server directly.

Each Wisp act as an intermediary for a singular entity, allowing users to authenticate without creating a direct path between the user and the system, and preventing compromise of other users.

Wisps update user accesses automatically to provide a seamless experience.

Wisps use commercially low-cost hosted micro-instances that can be destroyed during periods of inactivity.

Wisps enable secure collaboration with traditional and nontraditional partners by facilitating anonymous connections that protect sensitive information.
In any secured environment, users must authenticate with a server using some form of credentials to ensure they are who they say they are. But this carries an inherent risk since users and their devices must connect directly to the authentication server.
Wisps mitigate these risks by using commercial-hosted instances that bundle authentication information, tokens, and assigned access, acting as a messenger between the user and the central server so no association is created. When a user attempts to connect to a Fognigma using a Wisp, the Wisp instance reaches out to the Fognigma engine, ensures the connection is valid, and allows the user access.
In addition to avoiding risks inherent to traditional authentication methodologies, Wisp also serves as an ideal means of integrating mission partners, especially when trust is limited. Simply create a Wisp for the desired collaborator to provide them access limited strictly to where you need them—all while keeping the location of the central server secret. When access is no longer needed, an admin can instantly destroy the Wisp instance in a single click, eliminating the collaborator's only path to the resources.
TBD
Step 3 Description

Join thousands trusting Fognigma’s zero-trust networks for invisible, encrypted communication anywhere, anytime.